Specialized Keycloak consulting and an enterprise management platform — the two pillars of a well-running Keycloak in production.

These problems don't show up on day one. They surface when it's already in production.
Realms and flows left unchanged since the initial setup. Security gaps growing silently with every new user.
Events that vanish, no audit trail, compliance reviews that turn into fire drills.
Thousands of users, no bulk actions, no advanced filters, no history. Your team deserves better tooling.
Designed for regulated environments
For CTOs and tech leads who have already chosen Keycloak and need it to work exactly as their business requires.
Most Keycloak problems surface long after they start: poorly designed realms, default authentication flows left unchanged, upgrades that were never reviewed. We help you build it right from the start — or fix what's already there.
We design realms, flows, and themes that scale with your organization. A structured engagement with clear deliverables, documented and ready to go live.
Strong authentication without friction. We implement MFA that steps up only when the risk warrants it, tested end-to-end in your environment.
Systematic review of your instance against Keycloak's official security guidelines. Prioritized findings and an actionable remediation plan — not just a list of issues.
The enterprise management layer Keycloak needs but doesn't ship with.
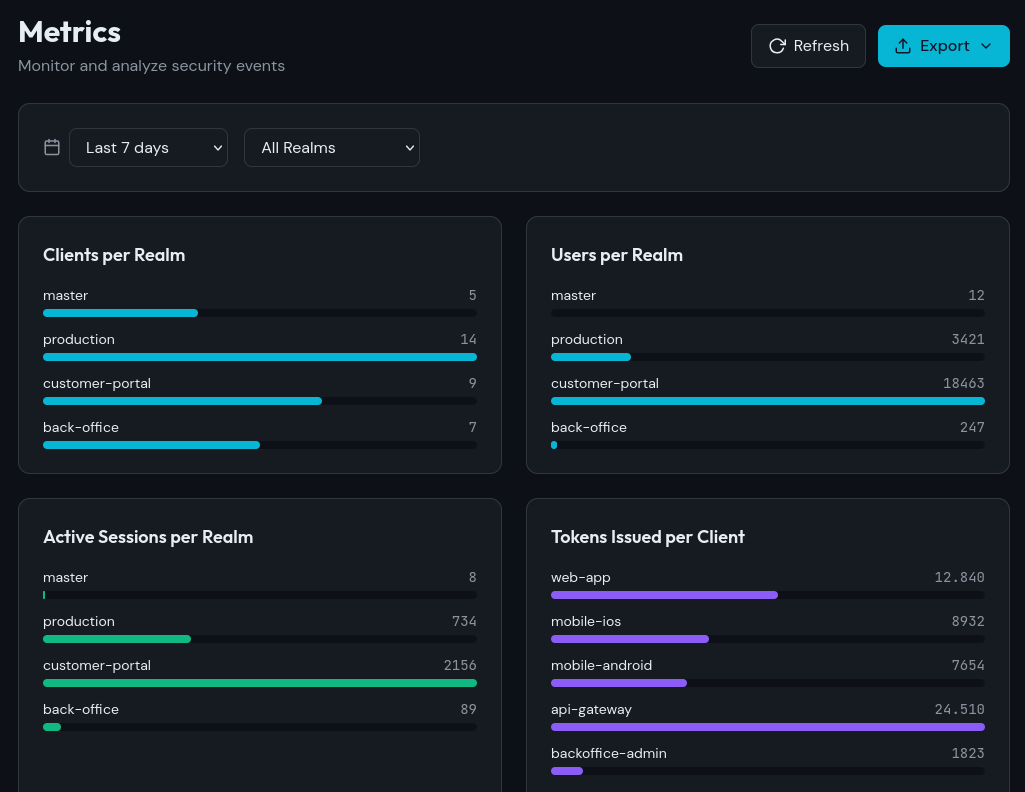
Keycloak is a solid foundation. Platform adds everything you need to operate it at enterprise scale: intelligent access control, advanced user management, and full observability. Without modifying your instance. Without custom development. With subscription plans.
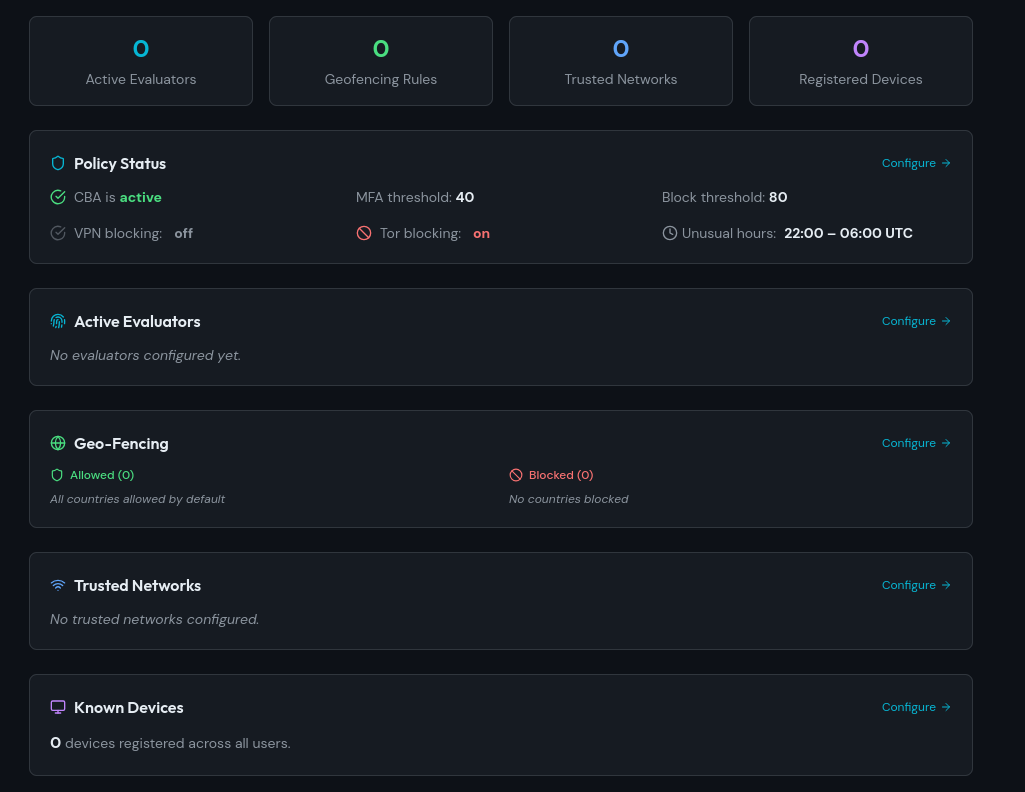
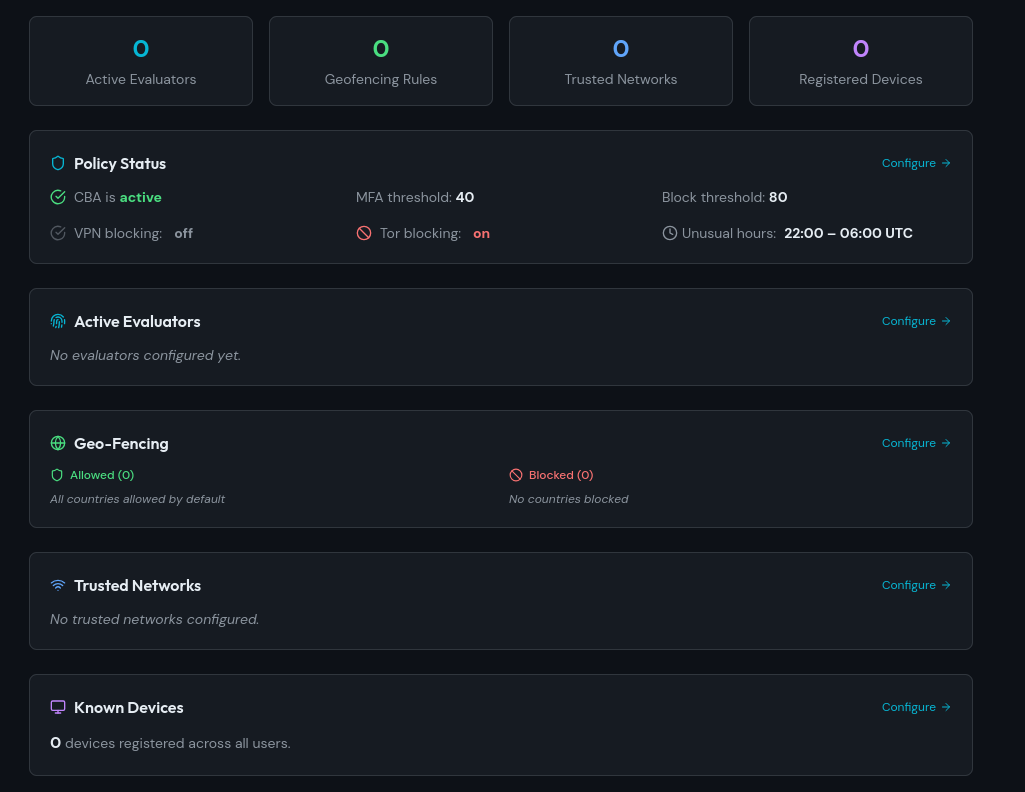
Secure your access based on real-time decisions.
Analyzes real-time signals from each login attempt — geolocation, IP reputation, device posture, user behavior — and evaluates them against a configurable risk matrix. Without relying solely on credentials that may be compromised.
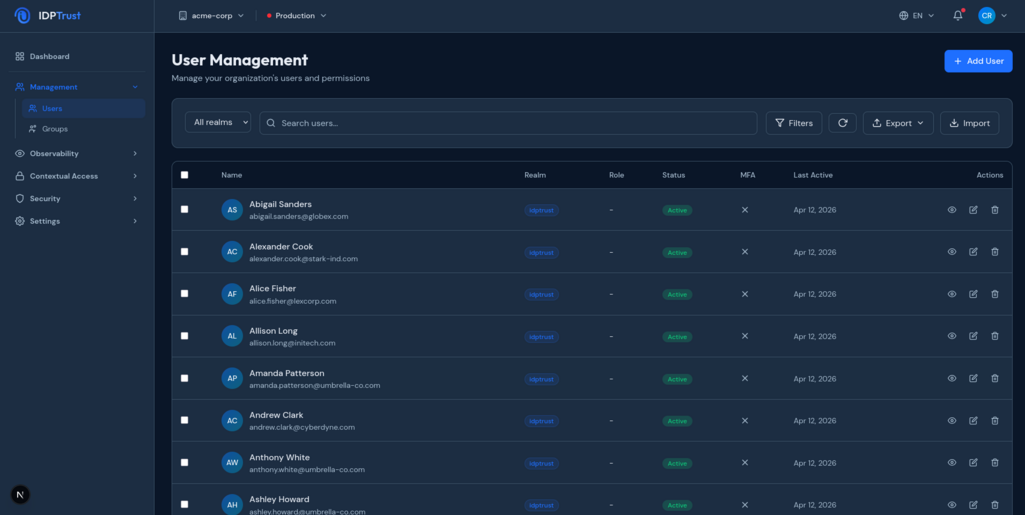
Full control over your users. No native console limitations.
Keycloak's console isn't built to manage thousands of users with custom attributes, automated offboarding flows, bulk actions, or historical records. Platform fills that gap with tools designed for operations and identity teams.
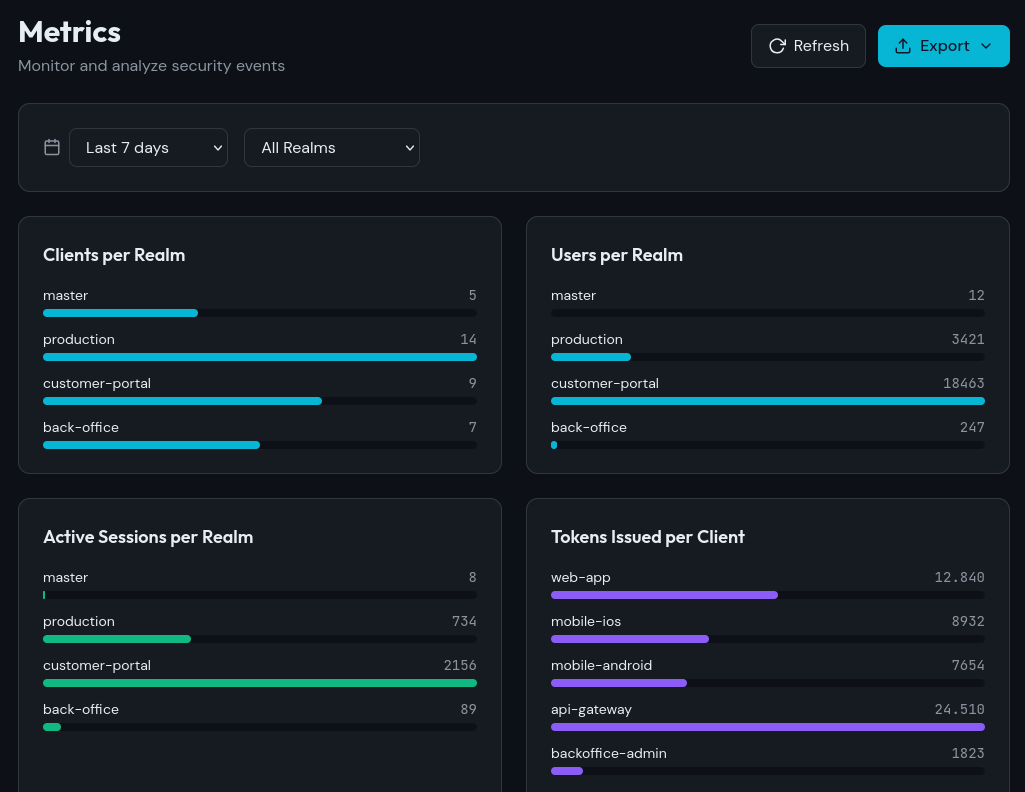
Know exactly what happened, when, and why.
Keycloak generates events but doesn't support their exploitation in enterprise environments or offer advanced search. Platform stores all events in a dedicated database, with human-readable descriptions and full traceability — regardless of whether the affected user or resource still exists.
We are a specialized team with enterprise experience, 100% focused on Keycloak. We don't do identity in general — we do Keycloak, done right.
Tell us about your use case and timelines. We respond within 24 hours.